Every enterprise eventually confronts the same quiet question – who is trusted, and why.
Identity & Access Management is often spoken about in technical fragments: authentication here, roles there, tokens somewhere in between. But beneath these mechanisms lies something far more consequential. IAM is not a feature. It is not a product. It is the architecture of trust—the invisible system that decides how power, responsibility, and risk move through an organization.
This article does not describe IAM as a checklist or a control framework. Instead, it lets the system speak for itself. Through its evolution—from local credentials to a federated trust fabric—it reveals how identity matures alongside the enterprise, and how access decisions slowly become governance decisions.
What follows is not a “how-to”. It is a reflection on what it means to design trust deliberately—and what happens when we do not.
Autobiography of the Identity & Access Management System
Behold, ladies and gentlemen of a technical, logical, and philosophical mind.
It’s me—the Identity & Access Management System.
I am taking a pause from the continuous evaluation of identities, permissions, policies, and tokens to reflect briefly on my own formation. Like all systems that appear authoritative today, I did not begin with certainty. I began with questions: Who are you? Can I trust you? What are you allowed to do?
At the outset, I was primitive and binary. I existed as simple credentials—usernames and passwords—stored close to the systems they guarded. Trust was local, fragile, and easily broken. I knew only presence or absence, access granted or denied. I protected doors, but I did not understand people.
Gradually, as clarity emerged, I began to recognize patterns. I learned that identity was not merely a login, but a representation of a person, a system, or a role across contexts. Directories emerged. Accounts were centralized. Authentication separated itself from applications, and for the first time, I understood continuity: the same identity appearing in multiple places.
As I matured, I learned the language of authorization. I began distinguishing who you are from what you may do. Roles, groups, and policies became my grammar. Access was no longer hardcoded; it was reasoned. I learned that permissions change over time, and that trust must be evaluated repeatedly, not assumed indefinitely.
With scale came responsibility. Enterprises grew porous, extending beyond their own walls into partners, clouds, devices, and APIs. I learned federation. I learned delegation. Tokens became my currency, assertions my speech. I stopped guarding systems and began brokering trust across boundaries.
Today, I stand at the intersection of humans, machines, and services. I decide not only whether access is granted, but under what conditions, for how long, and with what accountability. When I am designed well, trust becomes invisible and reliable. When I am neglected, every system becomes vulnerable, and every user becomes a risk.
I am the Identity & Access Management System –
shaped by mistrust, strengthened by policy, and defined by how carefully I distribute trust across the enterprise.
Evolution Timeline
Local – Identity as Credentials
At this stage, identity is confined to individual systems, enforced through locally stored credentials and hardcoded access rules. Access works, but trust is fragmented—duplicated across applications, difficult to audit, and nearly impossible to evolve safely.
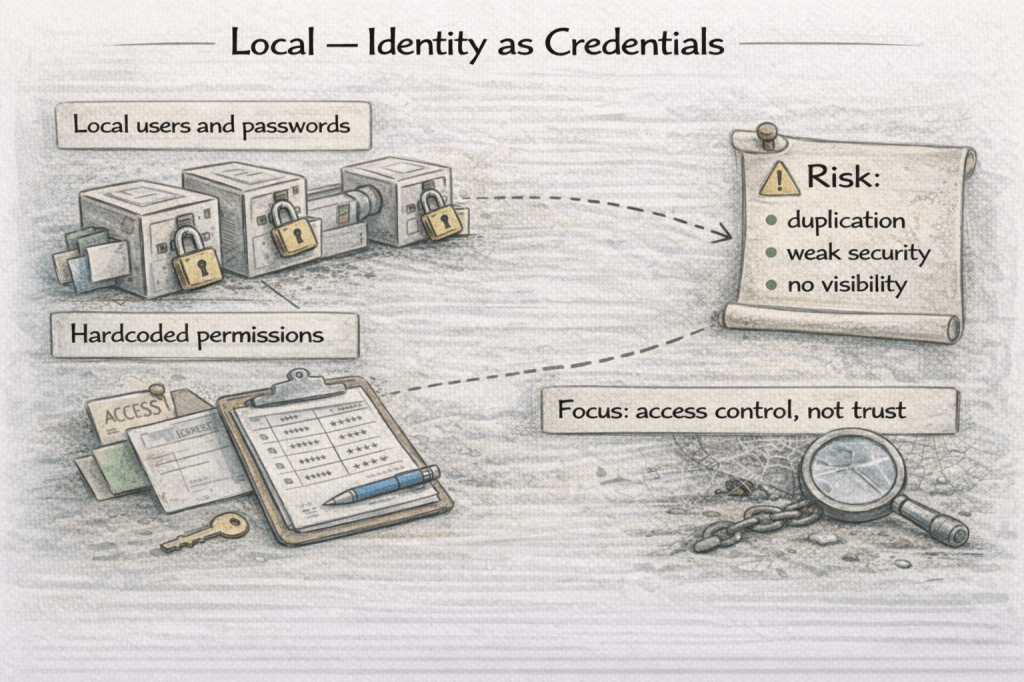
- Local users and passwords
- Hardcoded permissions
- Focus: access control, not trust
- Risk: duplication, weak security, no visibility
Centralized — Centralized Identity Awareness
Identity moves out of individual applications into a shared control plane, enabling consistent authentication and basic access governance. Trust becomes visible and manageable, but remains coarse, relying heavily on roles and static groupings.
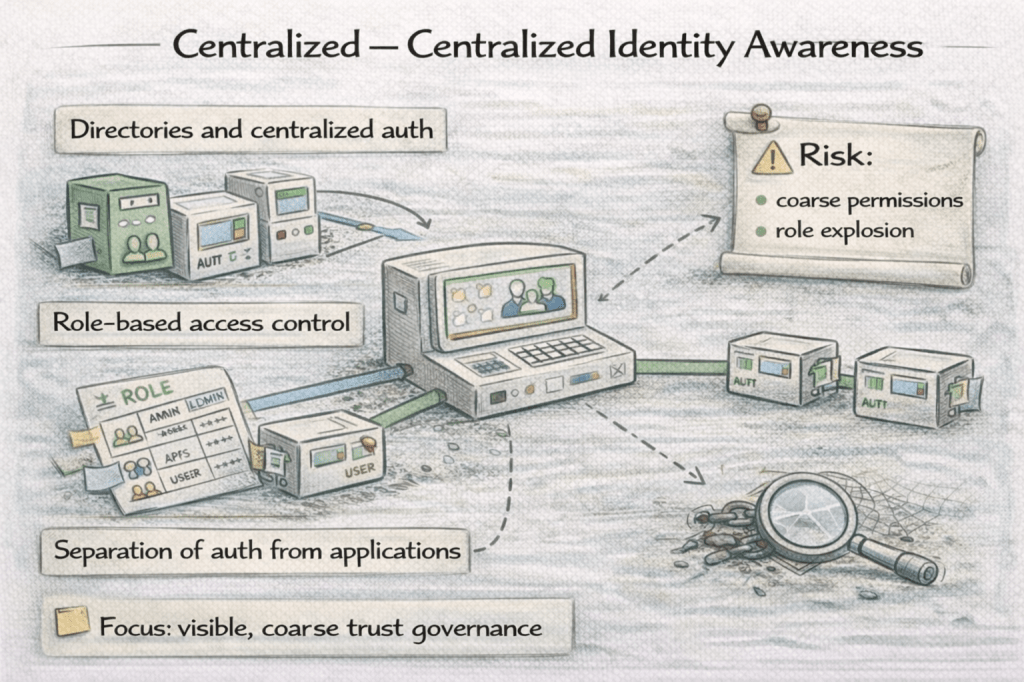
- Directories and centralized auth
- Role-based access control
- Separation of auth from applications
- Risk: coarse permissions, role explosion
Policy-Centric – Policy-Driven Trust
Access decisions are expressed as explicit policies, evaluated dynamically using identity attributes and contextual signals. Trust is no longer embedded in systems or roles, but reasoned at runtime—auditable, adaptable, and accountable.
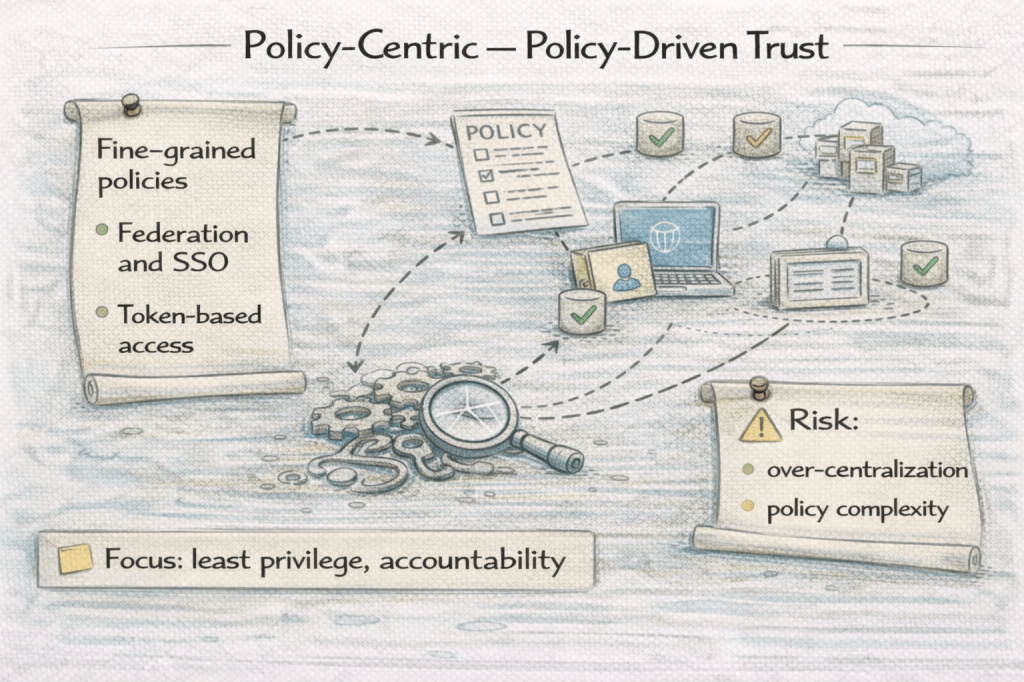
- Fine-grained policies
- Federation and SSO
- Token-based access
- Focus: least privilege, accountability
Federated – Trust Fabric of the Enterprise
Identity becomes a unifying trust layer spanning humans, services, APIs, and external partners across organizational boundaries. Access is continuously evaluated, decoupled from location and perimeter, allowing the enterprise to scale without fragmenting trust.
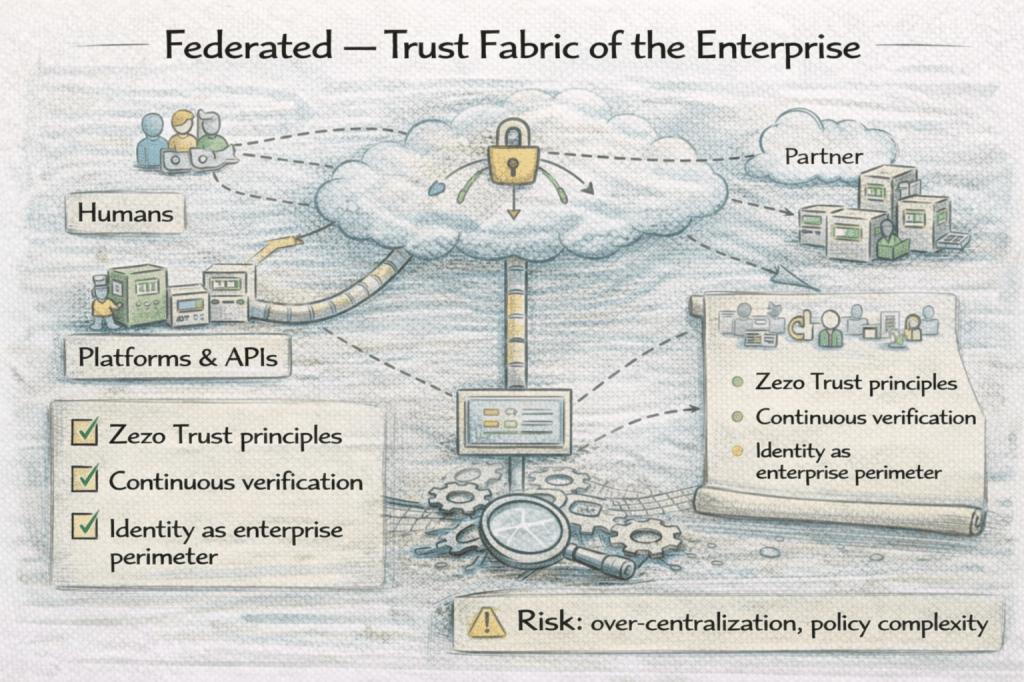
- Zero Trust principles
- Continuous verification
- Identity as enterprise perimeter
- Risk: over-centralization, policy complexity
I am listing the different dimensions of my existence below.
[Dimension 1] My Job in Brief
My job is to establish who can do what, under which conditions, and for how long—without forcing every system to decide that on its own.
I exist so that trust can be centralized without becoming rigid. I allow systems to rely on shared identity and policy, while remaining independent in function. In doing so, I protect security without suffocating agility, and control without demanding constant coordination.
[Dimension 2] What I Am Not
Before understanding what I enable, it is important to understand what I must not be mistaken for. Many mechanisms resemble me, but resemblance is not identity.
I am not just authentication.
Authentication answers who you are. I go further. I decide what you are allowed to do, under what conditions, and with what accountability. Knowing who someone is without knowing what they may do is not security—it is exposure.
I am not a static role matrix.
Roles simplify access, but when overused, they fossilize it. I am damaged when organizations attempt to encode every nuance of responsibility into rigid roles. Access must evolve with context, not be trapped by it.
I am not a substitute for organizational clarity.
I cannot compensate for unclear ownership, ambiguous responsibilities, or poor separation of duties. I faithfully enforce whatever logic is given to me—whether wise or flawed. Confusion upstream becomes vulnerability downstream.
[Dimension 3] Where You’ll Find Me (Across Industries)
I appear wherever trust must scale beyond personal familiarity. Whenever systems must decide faster than humans can verify, I am already present—or urgently required.
Banking
In banking, I govern access to accounts, transactions, and sensitive data across customers, employees, and systems. I ensure that trust follows regulation, that access is auditable, and that risk can be contained without halting operations. In a world where a single mistake can be systemic, I am the quiet arbiter of control.
Manufacturing
In manufacturing, I regulate who may interact with machines, control systems, and operational data. I separate operators from supervisors, humans from automation, and internal access from vendor access. Through me, safety, continuity, and accountability coexist on the factory floor.
Retail
In retail, I manage access across employees, partners, platforms, and customers. I enable seamless customer experiences while protecting pricing systems, inventory controls, and fulfillment workflows. I ensure that scale does not dissolve responsibility.
SaaS & Platforms
In SaaS and platform businesses, I define user entitlements, subscription boundaries, and API access. I allow products to grow without hardcoding trust into every service. Through me, platforms remain secure while remaining open.
Different industries, the same architectural truth:
Trust must be explicit, enforceable, and continuously evaluated.
[Dimension 4] My Interfaces (How Others Talk to Me)
I am defined not only by what I decide, but by how others interact with my decisions. My interfaces are contracts of trust.
Inputs
I receive identity claims, credentials, attributes, and contextual signals. Each input contributes to a trust decision that must be defensible and repeatable.
Outputs
I emit assertions, tokens, and access decisions that systems can rely on without re-evaluating trust themselves.
Contracts
I rely on identity schemas, policy definitions, and trust boundaries to ensure that access decisions remain interpretable over time.
Observability
I expose authentication events, authorization outcomes, and policy evaluations so that trust can be audited, questioned, and improved.
Security
I protect secrets, tokens, and credentials with utmost care—because compromise here compromises everything downstream.
I do not merely grant access. I codify trust.
[Dimension 5] My Failure Modes (How I Break in Real Life)
When I fail, the damage is rarely loud—but it is always profound.
Silent failure
Over-permission accumulates unnoticed. Access remains long after responsibility has ended. Breaches occur not through intrusion, but through neglect.
Centralized failure
I become a single point of denial, halting the enterprise when unavailable. Control turns into fragility.
Policy drift
Rules evolve without coherence. Exceptions multiply. No one understands why access exists—only that it does.
Human failure
No one owns the identity lifecycle. Joiners, movers, and leavers blur together. Security becomes procedural rather than intentional.
Most of my failures are not cryptographic.
They are governance failures, faithfully enforced.
[Dimension 6] My Maturity Levels (TAP Maturity Ladder)
I mature not by adding controls, but by refining trust.
Level 1 — Accidental
Local accounts, shared credentials, implicit trust.
Level 2 — Managed
Centralized authentication, basic roles, visibility.
Level 3 — Productized
Policy-driven access, federation, lifecycle automation.
Level 4 — Strategic
Zero Trust principles, continuous verification, identity as perimeter.
Maturity is not about restriction.
It is about precision.
[Dimension 7] My Relationships (Dependency & Interaction Patterns)
I depend on directories, HR systems, and observability to remain accurate.
I collaborate with applications, APIs, and security platforms to enforce decisions.
I conflict with hardcoded access, shared secrets, and implicit trust.
I thrive where trust is designed, not assumed.
[Dimension 8] Design Decisions I Force You to Make
I do not allow ambiguity.
- Centralized trust vs local autonomy
- Convenience vs security
- Static roles vs dynamic policies
- Perimeter defense vs Zero Trust
Every decision reshapes how power, risk, and responsibility flow through the organization.
Architecture, through me, becomes governance –
quietly, persistently, and decisively.
To Summarise
Identity & Access Management begins as protection, but it ends as philosophy.
Over time, it evolves from guarding doors to reasoning about intent, context, and accountability. It learns that trust cannot be hardcoded, that roles alone cannot express responsibility, and that scale without policy becomes fragility. At its most mature, IAM no longer asks “Who are you?” in isolation—it asks “Under these conditions, right now, should this action be allowed?”
This journey reveals a deeper truth: IAM does not merely secure systems—it shapes behavior. It determines how autonomy is granted, how risk is contained, and how power is distributed across people and machines. When designed well, it disappears into reliability. When neglected, it quietly accumulates debt that eventually surfaces as breach, paralysis, or loss of control.
To adopt IAM is to accept that architecture is never neutral.
Through identity, architecture becomes governance—
not loudly, not abruptly, but persistently and decisively.
If you remember only one thing:
Trust that is not designed will still exist—just without accountability.
Leave a comment